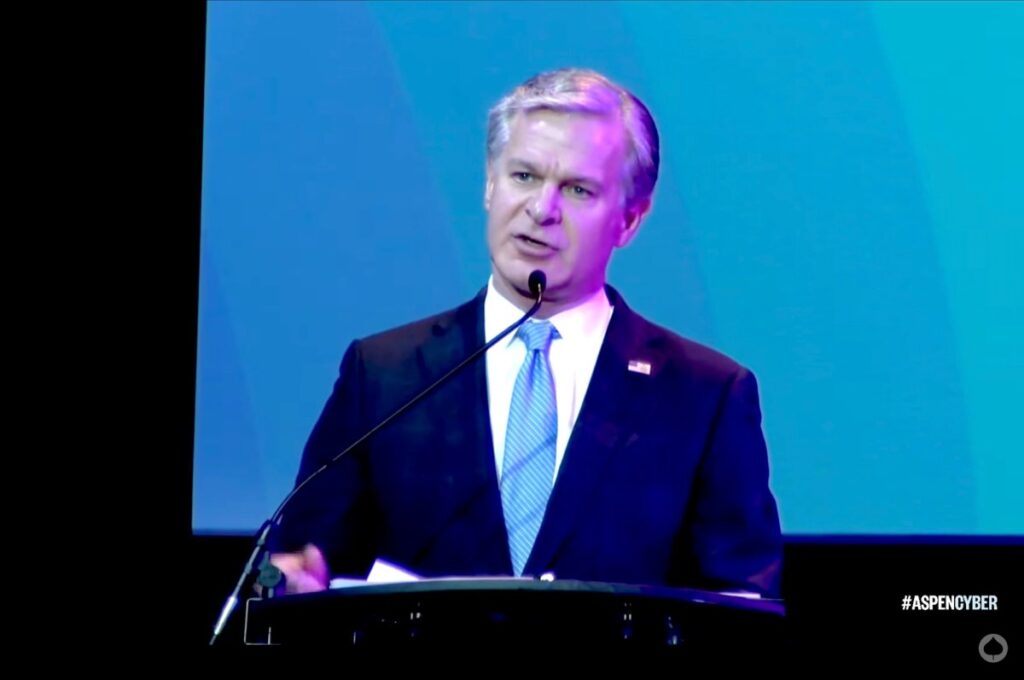
Last week, the FBI seized control of a botnet consisting of hundreds of thousands of internet-connected devices, including cameras, video recorders, storage devices and routers, that was run by a Chinese government hacking group, FBI Director Christopher Wray and US government agencies revealed on Wednesday.
The hacker group, named Flux Typhoon, “targeted critical infrastructure across the U.S. and abroad, from businesses and media organizations to universities and government agencies,” Wray said at the Aspen Cyber Summit, a cybersecurity conference, on Wednesday.
“But working with our partners, we conducted a court-authorized operation and seized the botnet's infrastructure,” Wray said, explaining that once the agency did so, the FBI also removed the malware from the compromised devices. “The bad guys realized what was going on and attempted to migrate the bots to new servers, which is where we started.” [Distributed Denial of Service] It's an attack on us.”
When contacted by TechCrunch on Wednesday, an FBI spokesperson declined to comment.
It is the latest U.S.-led effort against infrastructure linked to Chinese-backed hacking operations and cyberattacks as senior U.S. officials warn of Chinese efforts to inflict “real-world harm” on Americans in the event of a future conflict with China.
Contact Us Have more information about nation-state cyber attacks? You can securely contact Lorenzo Franceschi-Bicchierai from a non-work device via Signal (+1 917 257 1382), Telegram, Keybase @lorenzofb, or email. You can also contact TechCrunch via SecureDrop.
In a joint advisory released Wednesday, the FBI, the Cyber National Mission Force and the National Security Agency said the botnet that compromised 260,000 devices was linked to the Chinese government. The advisory said the botnet was used to conceal the activities of Chinese hackers. The U.S. government said the botnet was operated and controlled by Integrity Technology Group, which is said to work for the Chinese government.
Representatives for Integrity Technology Group did not respond to TechCrunch's request for comment on Wednesday.
According to the advisory, the botnet hacked vulnerable internet-connected devices using Mirai, a notorious piece of malware designed to control large numbers of compromised devices that was open-sourced in 2016 after a group of hackers used it to launch what was then the most powerful distributed denial-of-service attack.
Operation Flax Typhoon targeted a large number of internet-connected consumer devices, and authorities said they found a database of “more than 1.2 million compromised device records, including more than 385,000 victim devices in the United States that have been or are currently being exploited.”
 A table showing the number of IoT devices compromised by Flax Typhoon. (Image: Screenshot/US Government)
A table showing the number of IoT devices compromised by Flax Typhoon. (Image: Screenshot/US Government)
Microsoft released a report on Flax Typhoon earlier this year, stating that the group had targeted “dozens of organizations” in Taiwan. The tech giant reported that Flax Typhoon has been active since mid-2021, targeting “government agencies, education, critical manufacturing, and information technology organizations in Taiwan.”
Cybersecurity firm ESET wrote in a report published Wednesday that it observed Flax Typhoon compromise multiple Microsoft Exchange servers in Taiwan and “targeted multiple government agencies as well as consulting firms, travel booking software companies, and the pharmaceutical and electronics industries.”
Earlier this year, the U.S. government thwarted the activities of another Chinese government hacker group called Bolt Typhoon, which was actively targeting U.S. internet providers and U.S. critical infrastructure. The U.S. government said at the time that Bolt Typhoon was preparing to launch cyberattacks capable of causing devastating cyberattacks in the event of a future conflict with the United States, such as an expected Chinese invasion of Taiwan.